- Home
- Resources
Resource by Type

Security
CROWDSTRIKE 2025 GLOBAL THREAT REPORT
Security
CROWDSTRIKE 2023 GLOBAL THREAT REPORT
Cloud
10 Takeaways from Companies Who Have Migrated to Cloud

IBM i
Strategy and Roadmap Whitepaper
Get the executive guide to the strategy and roadmap for the IBM i integrated operating environment for Power Systems.
Learn how IBM i can help you transform your organization into a center for...
Cloud Services
Hybrid Cloud – What It Is, Why It Matters
As organizations attempt to strike a balance between having all IT services on-premises and offloading storage and compute to the cloud, a logical middle ground has emerged: the hybrid cloud.
This...

Security
Integrated Cybersecurity: Don’t Be the Next Ransomware Headline

Cloud
Cyverity Research Whitepaper by David Senf
Learn about the Cloud impact on IT Security in this whitepaper by David Senf, founder of Cyverity Research. Cyverity has conducted in-depth surveys and analysis to help organizations measure the...
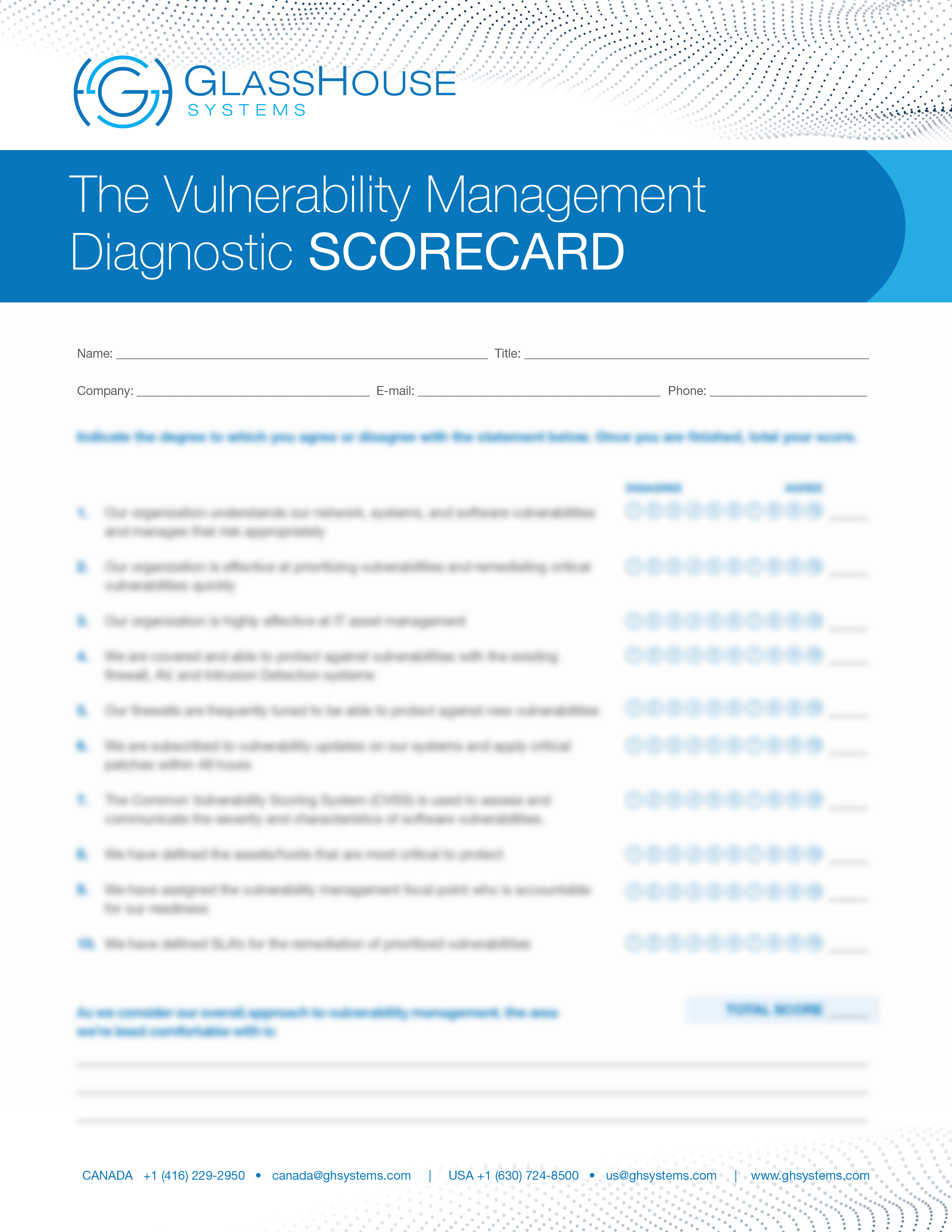
Security
The Vulnerability Management Diagnostic Scorecard
We’ve all heard the horror stories of what can happen when a hacker infiltrates your company. In the best-case scenario, you lose money, time, and trust. In the worst-case scenario, your company may...

BaaS
Addressing Business Risk While Overcoming Enterprise Backup Complexity
Palo Alto Next Generation Firewall Promotion by GlassHouse Systems
4 Reasons to Migrate to the Cloud in 2018

A global consumer products manufacturer recently completed a major modernization initiative by migrating its SAP ECC environment to IBM Cloud Power Virtual Server. The organization operated critical...

GlassHouse Systems helped an enterprise client unlock the full value of their existing cloud environment by transforming it from a basic hosting layer into a strategic growth platform. While the...

A growing software company offering sales engagement solutions was gaining momentum across mid-market and enterprise clients. Its platform, focused on outbound calling, CRM integration, automated...

A mid-stage SaaS company in the retail technology space has rapidly gained traction by helping online merchants increase cart conversion through AI-driven product discovery and personalized...

In the fleet compliance and telematics industry, companies operate in a regulation-heavy environment where digital log accuracy, real-time location data, and mobile-first experiences are essential....

A Use Case for High-Growth Companies in Private Equity Portfolios
For companies owned by private equity, growth is not a goal. It is a mandate. The pace is set from the boardroom, and the business...

In today’s financial world, software does not just support the business. It is the business. Clients expect their providers to deliver more than features. They expect reliability, scale,...

An Independent Software Vendor (ISV) serving the commercial construction industry engaged GlassHouse Systems (GHS) following a business-critical disruption that exposed fundamental limitations in its...

A multinational technology manufacturer operating in imaging, electronics, and industrial systems made the strategic decision to exit the VMware ecosystem. This decision was driven by financial...

In the competitive and high-pressure world of automotive auctions, where efficiency, reliability, and uptime are non-negotiable, a prominent independent software vendor (ISV) has begun a...

A large U.S.-based industrial distributor with over 360 users operating across domestic and international locations initiated a business-critical initiative to modernize its IBM i infrastructure and...

GlassHouse Systems (GHS) is pleased to announce an expansion of our Security Operations Center (SOC) and Managed Security offering with Google Security Operations. As cybersecurity threats grow in...


